.avia-section.av-av_section-22a228d159c734463cb33864c2febc68 .av-parallax .av-parallax-inner{
background-repeat:no-repeat;
background-image:url(https://www.frameworkit.com/wp-content/uploads/2023/11/Background_v2.png);
background-position:50% 50%;
background-attachment:scroll;
}
#top .hr.hr-invisible.av-av_hr-42e1a93dca9db7f8114d0c3d8caa7158{
margin-top:-150px;
height:1px;
}
.flex_column.av-av_three_fifth-c967d6da0b00f45c5cf215f8d125a565{
border-radius:0px 0px 0px 0px;
padding:0px 0px 0px 0px;
}
#top .av-special-heading.av-lyqamxkx-422db32477bc86de85932ad4d4b84a76{
padding-bottom:10px;
color:#ffffff;
}
body .av-special-heading.av-lyqamxkx-422db32477bc86de85932ad4d4b84a76 .av-special-heading-tag .heading-char{
font-size:25px;
}
.av-special-heading.av-lyqamxkx-422db32477bc86de85932ad4d4b84a76 .special-heading-inner-border{
border-color:#ffffff;
}
.av-special-heading.av-lyqamxkx-422db32477bc86de85932ad4d4b84a76 .av-subheading{
font-size:15px;
}
What Are the Security Threats Following Windows 10 End of Support?
#top .hr.hr-invisible.av-av_hr-d475a002bafe6afadfcf1a009695ce70{
height:15px;
}
#top .av_textblock_section.av-lyqan1xd-d2f60e6a1fc10cebb82b0616b41fb6a1 .avia_textblock{
color:#ffffff;
}
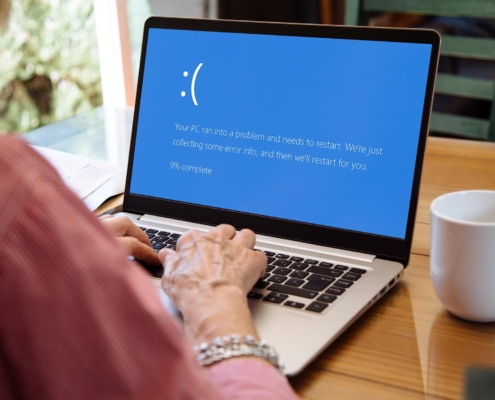
Hoping to continue using Windows 10 after its end of support on October 14, 2025? Hackers are constantly looking for weaknesses, and an outdated system is an open invitation for trouble. This blog will guide you through the security risks of an unsupported Windows 10 and offer ways to stay safe, even if upgrading isn’t an immediate option.
.flex_column.av-av_two_fifth-0c30ae0382806a7a1ef31702f9129c67{
transform:scale(1.2);
z-index:5;
border-radius:0px 0px 0px 0px;
padding:0px 0px 0px 0px;
}
@media only screen and (min-width: 480px) and (max-width: 767px){
.flex_column.av-av_two_fifth-0c30ae0382806a7a1ef31702f9129c67{
padding:10px 10px 10px 10px;
}
}
@media only screen and (max-width: 479px){
.flex_column.av-av_two_fifth-0c30ae0382806a7a1ef31702f9129c67{
padding:10px 10px 10px 10px;
}
}
box-shadow:none;
}
.avia-image-container.av-lyqauxb2-001f9b7755768189b723e649a404a596 .av-image-caption-overlay-center{
color:#ffffff;
}

.flex_column.av-g7p3g0k-b260164873e4a5e3000deb79a9224d6f{
border-radius:0 0 0 0;
padding:0 0 0 0;
}
#top .av-special-heading.av-i38q0wk-b920fc4295a8f6ae19a45a82a4d45483{
margin:0 0 0 0;
padding-bottom:0;
color:rgb(60, 67, 74);
}
body .av-special-heading.av-i38q0wk-b920fc4295a8f6ae19a45a82a4d45483 .av-special-heading-tag .heading-char{
font-size:25px;
}
.av-special-heading.av-i38q0wk-b920fc4295a8f6ae19a45a82a4d45483 .special-heading-inner-border{
border-color:rgb(60, 67, 74);
}
.av-special-heading.av-i38q0wk-b920fc4295a8f6ae19a45a82a4d45483 .av-subheading{
font-size:15px;
}
Thinking of Running Windows 10 Past Its End-of-Life Date?
#top .av_textblock_section.av-hkjlcd0-491641b1b789eacf71596ab942977963 .avia_textblock{
color:rgb(60, 67, 74);
}
A critical date for Windows 10 users is fast approaching: October 14, 2025. That’s when Microsoft will officially end support for this widely used operating system.
That also means no more updated security protecting your computer from malware, viruses, and other cyberattacks. These security features are like shields, constantly patching up vulnerabilities that hackers might try to exploit. But what happens when those shields disappear?
Let’s explore the security risks following Windows 10 end of support. We’ll walk you through the dangers, provide real-world examples, and even offer some advice on how to stay protected.
.flex_column.av-g7p3g0k-b260164873e4a5e3000deb79a9224d6f{
border-radius:0 0 0 0;
padding:0 0 0 0;
}
#top .av-special-heading.av-i38q0wk-4d32bd76012bc4812ea91d51b2d4546c{
margin:0 0 0 0;
padding-bottom:0;
color:rgb(60, 67, 74);
}
body .av-special-heading.av-i38q0wk-4d32bd76012bc4812ea91d51b2d4546c .av-special-heading-tag .heading-char{
font-size:25px;
}
.av-special-heading.av-i38q0wk-4d32bd76012bc4812ea91d51b2d4546c .special-heading-inner-border{
border-color:rgb(60, 67, 74);
}
.av-special-heading.av-i38q0wk-4d32bd76012bc4812ea91d51b2d4546c .av-subheading{
font-size:15px;
}
The Importance of Receiving Security Updates
#top .av_textblock_section.av-hkjlcd0-491641b1b789eacf71596ab942977963 .avia_textblock{
color:rgb(60, 67, 74);
}
Your computer’s operating system stores personal information, photos, and important documents. Security setting updates are like regular safety checks for a home, ensuring the doors, windows, and locks are all strong.
If they aren’t, weaknesses in the software could pose a serious security threat. It could be a gap in the code, a hidden backdoor, or even a misconfiguration. Just like a flimsy lock on your front door, these weak points make it easier for attackers to sneak in and wreak havoc.
Now, let’s take a look at the specific ways in which Windows 10 end of support can leave your business vulnerable.
.flex_column.av-g7p3g0k-b260164873e4a5e3000deb79a9224d6f{
border-radius:0 0 0 0;
padding:0 0 0 0;
}
#top .av-special-heading.av-i38q0wk-c6b53948a03b3d9577bfef31799ed503{
margin:0 0 0 0;
padding-bottom:0;
color:rgb(60, 67, 74);
}
body .av-special-heading.av-i38q0wk-c6b53948a03b3d9577bfef31799ed503 .av-special-heading-tag .heading-char{
font-size:25px;
}
.av-special-heading.av-i38q0wk-c6b53948a03b3d9577bfef31799ed503 .special-heading-inner-border{
border-color:rgb(60, 67, 74);
}
.av-special-heading.av-i38q0wk-c6b53948a03b3d9577bfef31799ed503 .av-subheading{
font-size:15px;
}
Windows 10 and Security Threats Following October 14, 2025
#top .av_textblock_section.av-hkjlcd0-491641b1b789eacf71596ab942977963 .avia_textblock{
color:rgb(60, 67, 74);
}
After its end-of-life date, Microsoft will officially stop releasing security updates for this popular operating system. Without updated security settings, your system becomes increasingly susceptible to a variety of security threats. Your once secure environment can become a hacker’s playground in the blink of an eye.
But what exactly are you up against? Here’s a detailed look into the specific security threats that lurk after Windows 10 end of support.
.flex_column.av-g7p3g0k-b260164873e4a5e3000deb79a9224d6f{
border-radius:0 0 0 0;
padding:0 0 0 0;
}
#top .av-special-heading.av-i38q0wk-ddcfb9be915d91290379863399fd2ad1{
margin:0 0 0 0;
padding-bottom:0;
color:rgb(60, 67, 74);
}
body .av-special-heading.av-i38q0wk-ddcfb9be915d91290379863399fd2ad1 .av-special-heading-tag .heading-char{
font-size:25px;
}
.av-special-heading.av-i38q0wk-ddcfb9be915d91290379863399fd2ad1 .special-heading-inner-border{
border-color:rgb(60, 67, 74);
}
.av-special-heading.av-i38q0wk-ddcfb9be915d91290379863399fd2ad1 .av-subheading{
font-size:15px;
}
Malware and Viruses Running Wild
#top .av_textblock_section.av-hkjlcd0-491641b1b789eacf71596ab942977963 .avia_textblock{
color:rgb(60, 67, 74);
}
If your computer is a vault filled with your precious digital belongings, the lock on that vault becomes rusty and unreliable without updated security. Malware, viruses, and especially ransomware will have a much easier time sneaking in and wreaking havoc.
Ransomware, in particular, can encrypt your entire hard drive, holding your data hostage until you pay a hefty ransom. These malicious programs thrive on unpatched vulnerabilities, and if you’re operating without the latest version of Windows, you’re an easy mark.
.flex_column.av-g7p3g0k-7dcf5b90a43edbd6470b1d108238b381{
border-radius:0 0 0 0;
padding:0 0 0 0;
}
#top .av-special-heading.av-i38q0wk-466dffafe014975b234c78e4d5185a14{
margin:0 0 0 0;
padding-bottom:0;
color:rgb(60, 67, 74);
}
body .av-special-heading.av-i38q0wk-466dffafe014975b234c78e4d5185a14 .av-special-heading-tag .heading-char{
font-size:25px;
}
.av-special-heading.av-i38q0wk-466dffafe014975b234c78e4d5185a14 .special-heading-inner-border{
border-color:rgb(60, 67, 74);
}
.av-special-heading.av-i38q0wk-466dffafe014975b234c78e4d5185a14 .av-subheading{
font-size:15px;
}
Zero-Day Exploits
#top .av_textblock_section.av-hkjlcd0-491641b1b789eacf71596ab942977963 .avia_textblock{
color:rgb(60, 67, 74);
}
Security experts are constantly working to identify and patch vulnerabilities in software. However, sometimes new vulnerabilities, called “zero-day” vulnerabilities, are discovered by hackers before developers or security firms can patch them.
With Windows 10 end of support, there will be no more patches to address these zero-day vulnerabilities. This leaves your operating system wide open to attacks that exploit these newly discovered weaknesses.
.flex_column.av-g7p3g0k-b260164873e4a5e3000deb79a9224d6f{
border-radius:0 0 0 0;
padding:0 0 0 0;
}
#top .av-special-heading.av-i38q0wk-4c235c02c2030012031b4b7324b19b9d{
margin:0 0 0 0;
padding-bottom:0;
color:rgb(60, 67, 74);
}
body .av-special-heading.av-i38q0wk-4c235c02c2030012031b4b7324b19b9d .av-special-heading-tag .heading-char{
font-size:25px;
}
.av-special-heading.av-i38q0wk-4c235c02c2030012031b4b7324b19b9d .special-heading-inner-border{
border-color:rgb(60, 67, 74);
}
.av-special-heading.av-i38q0wk-4c235c02c2030012031b4b7324b19b9d .av-subheading{
font-size:15px;
}
Targeted Attacks
#top .av_textblock_section.av-hkjlcd0-491641b1b789eacf71596ab942977963 .avia_textblock{
color:rgb(60, 67, 74);
}
Cybercriminals are becoming increasingly sophisticated, often targeting operating systems with known vulnerabilities. Businesses with valuable customer data or individuals with sensitive financial information become prime targets.
Without the protection of security updates for Microsoft Windows, your system becomes a bullseye for these targeted attacks. Attackers can exploit unpatched vulnerabilities to gain access to your system, steal your data, or even install malware that allows them to take control of your computer.
.flex_column.av-g7p3g0k-7247919f958a4a29f3134c7316cea408{
border-radius:0 0 0 0;
padding:30px 30px 30px 30px;
background-color:#eeeeee;
}
Empowering your team against cyberthreats takes more than updated software. Discover how email security strategies from Framework IT can keep your team communicating safely..
#top #wrap_all .avia-button.av-lyqana33-5a94709a4aaa10757eaa6437b2ed673c{
padding:15px 40px 15px 40px;
}
.flex_column.av-g7p3g0k-b260164873e4a5e3000deb79a9224d6f{
border-radius:0 0 0 0;
padding:0 0 0 0;
}
#top .av-special-heading.av-i38q0wk-45b0f72178794d54743b73b17240b80e{
margin:0 0 0 0;
padding-bottom:0;
color:rgb(60, 67, 74);
}
body .av-special-heading.av-i38q0wk-45b0f72178794d54743b73b17240b80e .av-special-heading-tag .heading-char{
font-size:25px;
}
.av-special-heading.av-i38q0wk-45b0f72178794d54743b73b17240b80e .special-heading-inner-border{
border-color:rgb(60, 67, 74);
}
.av-special-heading.av-i38q0wk-45b0f72178794d54743b73b17240b80e .av-subheading{
font-size:15px;
}
How to Mitigate Security Threats if Upgrading Isn’t Possible
#top .av_textblock_section.av-hkjlcd0-491641b1b789eacf71596ab942977963 .avia_textblock{
color:rgb(60, 67, 74);
}
Upgrading to a supported operating system might not be immediately feasible for everyone. There could be hardware compatibility concerns, budgetary limitations, or simply a need for more time to plan the transition.
While upgrading is the ultimate solution for long-term security, there are some steps you can take to mitigate risks while you plan your next move:
- Keep Everything Updated (But Know the Limits): While Microsoft won’t be patching Windows 10 itself, software developers will likely continue to release security updates for their own programs (e.g., web browsers, productivity applications). Make sure to keep all your software updated to the latest versions to address vulnerabilities specific to those programs. However, these application updates won’t plug the holes in the core Windows 10 operating system itself.
- Strong Antivirus and Firewall: Consider investing in a robust antivirus and firewall solution. These tools can help detect and block some malicious software, but it’s important to understand their limitations. No antivirus protection is foolproof, and they may not be able to catch everything, especially zero-day attacks.
- Be Extra Cautious Online: Exercise extreme caution when browsing the internet. Phishing emails and malicious websites are common ways attackers exploit vulnerabilities. Don’t click on suspicious links or open unknown attachments in emails. Be wary of downloading software from untrusted sources, as these could be bundled with malware.
- Regular Backups are Crucial: With the increased risk of data breaches and ransomware attacks, regularly backing up your important data becomes even more critical. Consider implementing a backup schedule and storing your backups on an offline device to ensure your data is safe even if your computer is compromised.
Remember, these mitigation strategies are like putting on a raincoat in a hurricane. They might offer some temporary protection, but they’re not a long-term solution. Upgrading to a supported operating system like Windows 11 is the best way to ensure your system remains secure after Windows 10 end of support.
.flex_column.av-g7p3g0k-b260164873e4a5e3000deb79a9224d6f{
border-radius:0 0 0 0;
padding:0 0 0 0;
}
#top .av-special-heading.av-i38q0wk-c4c90f0c3cd8cd9c8aa932017bfd8d48{
margin:0 0 0 0;
padding-bottom:0;
color:rgb(60, 67, 74);
}
body .av-special-heading.av-i38q0wk-c4c90f0c3cd8cd9c8aa932017bfd8d48 .av-special-heading-tag .heading-char{
font-size:25px;
}
.av-special-heading.av-i38q0wk-c4c90f0c3cd8cd9c8aa932017bfd8d48 .special-heading-inner-border{
border-color:rgb(60, 67, 74);
}
.av-special-heading.av-i38q0wk-c4c90f0c3cd8cd9c8aa932017bfd8d48 .av-subheading{
font-size:15px;
}
Key Takeaways
#top .av_textblock_section.av-hkjlcd0-491641b1b789eacf71596ab942977963 .avia_textblock{
color:rgb(60, 67, 74);
}
Windows 10 end of support on October 14, 2025 marks a critical turning point for security threats. Here’s a quick recap of the main points to remember:
- No More Security Updates: After this date, Microsoft will stop releasing security updates for Windows 10, leaving your system vulnerable to known and unknown exploits.
- Increased Malware and Virus Risk: Unpatched vulnerabilities become open doors for malware, viruses, and ransomware to wreak havoc on your system.
- Targeted Attacks Become Easier: Without security updates, your Windows 10 operating system becomes a prime target for attackers looking to steal data or take control of your computer.
Upgrading to the latest version of Windows is the ultimate solution. However, if it’s not an immediate possibility, consider these steps:
- Keep Software Updated (Browsers, Applications): Patch vulnerabilities in other programs you use.
- Strong Antivirus and Firewall: Offer some protection, but have limitations.
- Be Cautious Online: Don’t click suspicious links or download from untrusted sources.
- Regular Backups are Essential: Protect your data in case of attacks.
.flex_column.av-g7p3g0k-b260164873e4a5e3000deb79a9224d6f{
border-radius:0 0 0 0;
padding:0 0 0 0;
}
#top .av-special-heading.av-i38q0wk-54e7e0558526991b785e0148582b3a95{
margin:0 0 0 0;
padding-bottom:0;
color:rgb(60, 67, 74);
}
body .av-special-heading.av-i38q0wk-54e7e0558526991b785e0148582b3a95 .av-special-heading-tag .heading-char{
font-size:25px;
}
.av-special-heading.av-i38q0wk-54e7e0558526991b785e0148582b3a95 .special-heading-inner-border{
border-color:rgb(60, 67, 74);
}
.av-special-heading.av-i38q0wk-54e7e0558526991b785e0148582b3a95 .av-subheading{
font-size:15px;
}
Prepare for Windows 10 End of Support With Professional Help From Framework IT
#top .av_textblock_section.av-hkjlcd0-491641b1b789eacf71596ab942977963 .avia_textblock{
color:rgb(60, 67, 74);
}
Upgrading your systems can feel like a daunting task, but you don’t have to do it alone. Here at Framework IT, we’re experts in cybersecurity and operating system migrations. Our team can help you navigate the entire process.
From assessing your current setup to planning and executing a smooth transition, we’ve got you covered. We’ll also ensure your new system is equipped with robust cybersecurity solutions to keep you protected from evolving threats.
We offer flexible solutions to fit your budget and timeline, ensuring a seamless migration with minimal disruption to your business operations. Contact us today for a free consultation and let us help you stay secure.
#top .av-special-heading.av-27roql0-975f4419869e21c89d72c1a9440d82d2{
padding-bottom:10px;
}
body .av-special-heading.av-27roql0-975f4419869e21c89d72c1a9440d82d2 .av-special-heading-tag .heading-char{
font-size:25px;
}
.av-special-heading.av-27roql0-975f4419869e21c89d72c1a9440d82d2 .av-subheading{
font-size:15px;
}
Share This Post
#top .av-special-heading.av-lfl9x42e-9ef0fa6f21463451fd83f52690716a72{
padding-bottom:30px;
}
body .av-special-heading.av-lfl9x42e-9ef0fa6f21463451fd83f52690716a72 .av-special-heading-tag .heading-char{
font-size:25px;
}
.av-special-heading.av-lfl9x42e-9ef0fa6f21463451fd83f52690716a72 .av-subheading{
font-size:15px;
}
More Like This
https://www.frameworkit.com/wp-content/uploads/2024/07/Windows-computer-crash.jpg
1250
2000
Abstrakt Marketing
https://frameworkit.com/wp-content/uploads/2023/11/logo.png
Abstrakt Marketing2024-07-15 12:59:072024-07-17 13:16:08What You Need to Know to Be Prepared for Windows 10 End of Life

https://www.frameworkit.com/wp-content/uploads/2024/07/Side-view-of-two-IT-professionals-looking-at-tablet-together.jpg
1250
2000
Abstrakt Marketing
https://frameworkit.com/wp-content/uploads/2023/11/logo.png
Abstrakt Marketing2024-07-05 14:19:402024-07-17 13:16:08Questions to Ask a Managed Services Provider

https://www.frameworkit.com/wp-content/uploads/2024/06/What-a-Virtual-CIO-Can-Bring-to-Your-Business.jpg
1250
2000
Abstrakt Marketing
https://frameworkit.com/wp-content/uploads/2023/11/logo.png
Abstrakt Marketing2024-06-13 13:13:502024-07-17 13:16:08What a Virtual CIO Can Bring to Your Business

https://www.frameworkit.com/wp-content/uploads/2024/06/Side-view-of-a-man-typing-on-laptop-keyboard.jpg
1250
2000
Abstrakt Marketing
https://frameworkit.com/wp-content/uploads/2023/11/logo.png
Abstrakt Marketing2024-06-13 12:03:232024-07-17 13:16:09Harnessing the Power of Microsoft Copilot and How to Prepare for Deployment

https://www.frameworkit.com/wp-content/uploads/2024/05/Close-up-hands-typing-using-laptop-computer.jpg
1250
2000
Abstrakt Marketing
https://frameworkit.com/wp-content/uploads/2023/11/logo.png
Abstrakt Marketing2024-05-22 15:01:232024-07-17 13:16:09Transitioning Your Business Between G Suite and Microsoft 365: A Comprehensive Guide

https://frameworkit.com/wp-content/uploads/2023/11/logo.png
0
0
Brandyn Fadler
https://frameworkit.com/wp-content/uploads/2023/11/logo.png
Brandyn Fadler2024-04-23 12:22:302024-04-23 12:22:34Mobile ConnectUC

https://frameworkit.com/wp-content/uploads/2023/11/logo.png
0
0
Brandyn Fadler
https://frameworkit.com/wp-content/uploads/2023/11/logo.png
Brandyn Fadler2024-04-23 09:09:482024-04-23 09:32:56Desktop ConnectUC

https://www.frameworkit.com/wp-content/uploads/2024/04/Side-view-of-two-employees-being-helped-by-an-IT-Professional.jpg
1250
2000
Abstrakt Marketing
https://frameworkit.com/wp-content/uploads/2023/11/logo.png
Abstrakt Marketing2024-04-17 10:37:532024-07-17 13:16:09Finding a Top Managed Services Provider in Chicago: A Comprehensive Guide

https://www.frameworkit.com/wp-content/uploads/2024/03/8-Cybersecurity-Solutions-to-Safeguard-Your-Remote-Workforce.jpg
1250
2000
Abstrakt Marketing
https://frameworkit.com/wp-content/uploads/2023/11/logo.png
Abstrakt Marketing2024-03-15 10:38:502024-07-17 13:16:098 Cybersecurity Solutions to Safeguard Your Remote Workforce
The post What Are the Security Threats Following Windows 10 End of Support? appeared first on Framework IT.